In this advanced world and modern technology, everyone has an approach to the internet. You can have easy access to every piece of information through it. But the work of Technology wolf is playing an essential role.
Along with the beneficial aspects of the internet, some widespread threats point to the misuse of the internet. Thus, it has become imperative to take care of the minor details, and for this purpose, things like technology wolf have become essential.
Fundamentals of Technology wolf
Many people are well familiar with the primary and leading brands that also come up with various security services. The work of technology wolf is one of the tremendous efforts that have crossed multiple minds.
They are running the business for about 25 years. Undoubtedly, it is a very long experience and has accomplished because of the technologists’ struggle.
They are mainly experts in ethical hacking and have different servers that can save you and can increase your interest to a great extent.
Along with the benefits and advantages of the internet, it is also essential to take crucial things and reach you towards different serious results.
The technology wolf offers some primary services to its company to facilitate them in several ways. Some of them magnified as follows:
- Security evaluation services for social engineering techniques
- Ethical hacking.
- Completely automated vulnerability scanning.
- Computer forensics.
Furthers details related to each aspect of the listed legal factors explained as:
Security evaluation services for social engineering techniques
The security evaluation services majorly made to understand different aspects of this social potential. There is mainly assessing another type of organization specifically created to realize the essential risk linked with human threats.
It can also further lead to different exposure or problems related to the people or any other infrastructure system. The work of technology wolf helps various organizations or bands understand that Social Security is their first preference.
There are different identifying tests and others that are preferred to secure Social Security. Many companies now become able to take the necessary actions taken at the time.
Ethical Hacking
There is no doubt in the fact that precautions are better than treatment. Various hackers in the market always try to grab the system in their hands. It is done by breaking the security system and having access to confidential files.
But in this scenario, it is utterly ethical as the organization’s help to make a hacker-free environment from entering the system. It allows a smooth approach to run without inconveniences for the people to secure their security purposes and come up with other benefits.
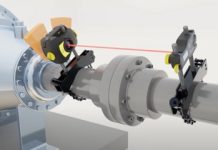
Automated vulnerability scanning
This step made to secure you without having any problem as it covers you in a protective sheet to prevent different threats. A common mechanism of it’s working can be estimated by the working of the scanner.
It is entirely safe as it modifies the changes in a single jerk. With the help of it alerts the organization, towards a great deal of awareness. For instance, if a person faces any threat, it quickly detects the system.
Due to its large number of beneficial aspects, it is a very advanced system. The process is vulnerable and acceptable in the people’s demand because of its high-security level.
The work of technology wolf allows the system or organization’s servers to work quickly to protect you from any further problems. The wolf technology acts as fast technology to protect you from different kinds of errors or problems.
It can raise its functionality above different kinds of leading brands or organizations. It has increased the demand level to secure you without causing any harm.
Computer forensics
Technology wolf is mainly a protectant to you when the hackers are using electronic media to approach or access your data in any way. It provides you with safe sided to protect from different kinds of unusual happenings that take place.
It prevents the higher rate of unlawful activity and reduces scammers’ risk and hacking from your organization or device. So, it made for your safety and protection. Your files may get protected from any further problems.
Final Verdict
After reading every line of the article, I hope you are well familiar with different aspects of how to work technology wolf.
It highlighted that it is entirely safe and non-toxic to your data or device. Although it prevents you from different kinds of further inconveniences that magnified as follows:
- Scamming
- Hacking.
- Threats.
- Fraud
To have a smooth-running organization or system, you must have proper management that may look after any scam or any other threat recorded in your work.
It mainly comes up in the market with a very advanced system and the latest ideas for different modifications. It not only makes you alert but also helps to secure your data for a lifetime.
You may not have any risk of hacking or any further inconveniences that may harm you, your device, or anything else. Now the system of many unethical activities has become very common, and such things regulated by the systems that make your organization far away from progress.
So, to avoid all such inconveniences and run a very high-rated organization Technology wolf is playing an essential role. , you need to join such technology. It not only gives you a guarantee and assurance for complete security coverage.
Your credential files or data management is their priority to prevent any negative aspects and offers many services. Because of its beneficial expect, it makes the system completely free from any future risk or problems.